After the Notary’s Seal: How to Build Document Authenticity That Holds Up Over Time
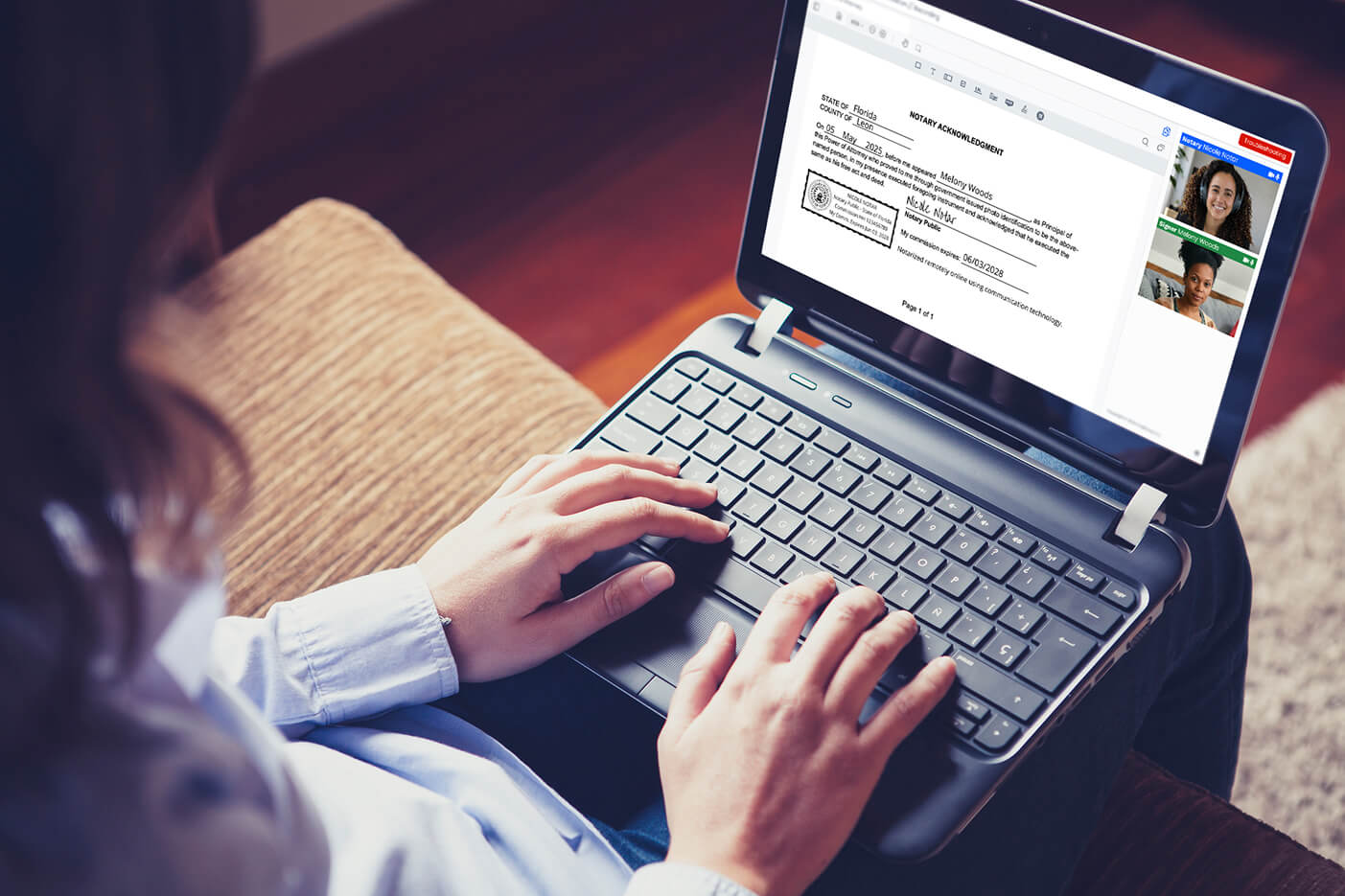
A notarial act is one of the most precise things that happens in document workflows. In the span of a single session — whether across a desk or over a secure video call — a commissioned notary verifies an identity, witnesses a signing, confirms intent, and creates a permanent record of the act. It is a moment of legal certainty in a world that increasingly lacks them.
But here is the question that keeps risk officers, title agents, and law firms awake at night: what happens to that document for the months and years after the session ends?
The notarial act proves what happened in the room. It is not designed to prove what happens to the document afterward — when it is emailed, photocopied, uploaded into a portal, downloaded from a portal, attached to a filing, archived, retrieved, forwarded, and re-presented years later. That window — between the moment of notarization and every subsequent moment when someone needs to confirm the document is still the document — is where modern fraud lives.
This article walks through the fraud landscape notaries and their clients are now operating in, where notarization’s protection ends and another layer needs to begin, and what a complete document trust architecture looks like in practice.
The fraud landscape has changed
Document fraud used to be the domain of skilled forgers with steady hands and good printers. That is no longer the world we are in.
The latest industry data tells a story most notaries already sense from their own caseloads. Resistant.ai’s Global Document Fraud Report 2026 analyzed over 170 million documents and found that one in three documents showed evidence of structural integrity tampering, with nearly one in ten showing tampering consistent with fraudulent intent — a category that grew 28.5% year over year. Sumsub’s Identity Fraud Report 2025–2026 recorded a 180% year-on-year rise in multi-step fraud attacks, where bad actors stitch together coordinated stages rather than relying on single fake documents.
AI is the accelerant. AI-assisted document forgery rose from essentially zero in 2024 to 2% of all fake documents detected in 2025, with generative AI fraud growing 90% year over year. Shufti recorded a 230% spike in deepfake ID attempts in a single quarter of 2025. The barrier to entry has collapsed: the average cost to access document fraud infrastructure in 2025 was $28.29 — less than a decent dinner.
For notaries, the immediate fraud surface during a session is reasonably well-managed by RON identity verification stacks: credential analysis, knowledge-based authentication, biometric checks, session recording. The session is the safest part of a document’s life. The danger is what happens to the file once it leaves the journal.
What notarization proves — and what comes next
It is worth being precise about what a notarial act actually attests to, because the precision is what makes it valuable.
A notary’s seal proves:
- A specific, identified person appeared (physically or via approved audio-video technology)
- That person signed a specific document in the notary’s presence
- The signer understood what they were signing and acted voluntarily
- The act occurred on a specific date, recorded in the notary’s journal
A notary’s seal does not — and was never intended to — prove:
- That a copy circulating six months later is identical to the document the notary witnessed
- That a PDF labeled “the notarized version” is actually the notarized version
- That a scan submitted to a third party hasn’t had a clause edited between the notary’s session and the moment of submission
- That a document presented years later still carries the same content as the original
These aren’t gaps in notarization. They are simply outside the scope of what a notarial act is designed to do. The notarial seal is a snapshot of an event. What protects the document between events is a different category of tool entirely — what the industry generally calls document authenticity or tamper-evidence.
Three scenarios where the post-notarization gap matters
The gap is easiest to see in concrete cases.
Scenario one: the altered closing package. A title company conducts a remote online notarization for a refinance. The session is clean, the recording is archived, the digital seal is applied. Six weeks later, an internal compliance review pulls the notarized package from a shared drive to confirm a disclosure clause. The clause has been edited. Was the change made before or after notarization? Without an independent integrity layer on the file itself, the only way to answer that is to retrieve the notary’s session recording and the original journal entry, hash the original artifact, and compare. That is a multi-day, multi-party investigation for what should be a five-second question.
Scenario two: the resubmitted power of attorney. An attorney’s office holds a notarized durable power of attorney for an elderly client. Two years later, a family member presents what they claim is the same notarized POA to a bank to release funds. The notarization metadata looks correct. The seal is there. But the asset transfer authority appears broader than the original document the attorney remembers drafting. Was the document modified? Is this a forgery built on a real notary seal? Without an issuer-controlled verification endpoint that the bank can scan and confirm against, the bank has to either accept the document at face value, contact the notary’s commission, or send it back to the attorney for written confirmation — slowing what should be a routine release.
Scenario three: the cross-border verification request. A US business notarizes a corporate authorization for use in an overseas transaction. The receiving party in another jurisdiction has no efficient way to confirm that the document they received by email is the same document the US notary actually witnessed. They request a fresh notarization. The original notarial act — perfectly valid in the US — does no work for the overseas counterparty because there is no portable, instant verification mechanism attached to the document itself.
In each case, the notarization was correct. What failed was everything after the notarization.
How modern document authenticity actually works
The good news is that the tools to close this gap are mature, standardized, and increasingly easy to integrate into document workflows. Here is the basic vocabulary, kept practical.
Cryptographic hashing. When a document is finalized, a hashing algorithm produces a unique fingerprint — a string of characters that changes completely if any part of the document is altered, even by one character. Hashing is the foundation of every tamper-evidence system. The hash itself doesn’t protect the document; it just makes any change immediately detectable.
Digital signatures. A digital signature uses cryptographic keys to bind the hash to an issuer. When someone receives the document later, they can verify two things at once: that the document hasn’t been altered (the hash still matches) and that it was issued by the party whose key signed it.
Verifiable QR codes. A QR code on a document — when implemented properly — doesn’t just contain text. It points to an issuer-controlled endpoint that returns the authoritative version, the original hash, and the issuance record. Anyone with a phone can verify the document in seconds. The QR code itself can’t be forged usefully, because a fake code wouldn’t resolve to the genuine issuer’s endpoint.
Anchored or registered records. For high-value documents, the issuance record can be anchored to an append-only registry — sometimes a public ledger, sometimes a private one — that makes the record itself tamper-evident. Even an attacker who somehow compromised the issuer’s systems couldn’t quietly alter past records.
Layered together, these tools answer the question is this document still the document? — a question notarization, by design, does not address.
What this means for notaries
For notaries, particularly those operating in RON environments, the practical implication is that the digital artifact you produce is the start of a longer chain. A few suggestions for staying ahead:
- Understand what your platform stores. Know how long your RON platform retains the session recording and the signed audit trail, what format the notarized document is delivered in, and what guarantees (if any) the platform makes about the integrity of downstream copies. These vary significantly across providers.
- Talk to clients about post-session document handling. Many disputes that look like notarial issues are actually post-session document handling issues. A short conversation at the end of a session — “here is the official version, here is how to verify it later” — saves a lot of downstream work.
- Recognize when a verification layer is warranted. For one-off personal documents, the notarial record is usually sufficient. For documents that will circulate widely, cross borders, or be re-presented years later, recommend that the issuing party add an authenticity layer on top of the notarial act. This isn’t a critique of notarization; it’s recognition that different threats need different defenses.
What this means for businesses using notarization
For law firms, title companies, lenders, insurers, and any organization for which notarized documents are a regular part of operations, the implication is architectural. The right question is not should we notarize or verify? It is how do we ensure the documents we produce remain trustworthy at every point they are touched, scanned, sent, or stored?
The answer is almost always a layered workflow:
- Notarize where the law or counterparty requires it — increasingly via RON for efficiency, with platforms like the one hosting this article making that practical at scale.
- Issue the notarized document with an authenticity layer attached — a verifiable QR code, a cryptographic hash registered to an issuer endpoint, or both.
- Make verification trivial for downstream recipients — anyone holding the document should be able to confirm authenticity in seconds, without contacting the issuer.
- Retain the records that prove both layers — the notarial journal entry and recording on one side, the issuance record and integrity proofs on the other.
This is the architecture our team at VerifyDoc.ai builds for organizations whose documents need to remain verifiable after the notarial session ends — and it pairs especially well with the RON workflows OneNotary’s readers are already running. The notary handles the moment of signing. The verification layer handles the years that follow. Together, they cover the whole life of the document.
The bottom line
The traditional model treated notarization as the final word on document trust. In a world of 244% year-over-year digital forgery growth and $28 entry-level fraud kits, that model is incomplete — not because notarization is weaker, but because the threats have moved into the gaps notarization was never designed to cover.
The notary’s seal is the start of the trust chain. What protects the document from the seal forward is a different layer of the same architecture. The organizations getting this right in 2026 are running both — and recognizing that, in this environment, document trust is no longer one act but a continuous property.
About the author: This guest post was written by the team at VerifyDoc.ai, which builds the document authenticity and tamper-evidence layer used by organizations that need their documents to stay verifiable long after issuance. For workflows that combine notarization with ongoing verification, get in touch at verifydoc.ai.